SOCIAL ENGINEERING
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
ADVERTISING
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
AI
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
BRANDING
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
AD FILM
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
CASE STUDY
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
CONTENT CREATION
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
DESIGNER VS CLIENT
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
DIGITAL MARKETING COURSES
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.
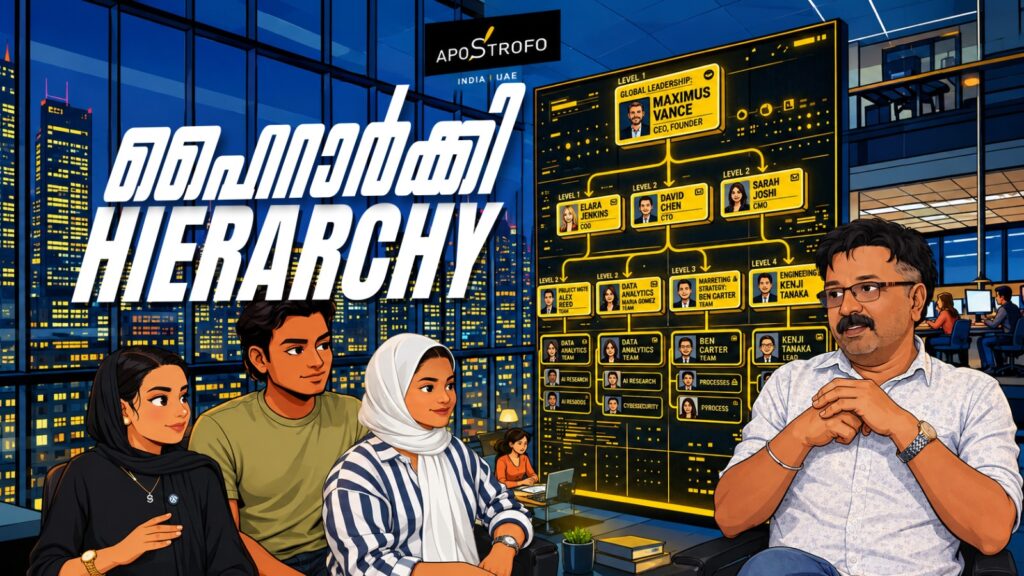
HIERARCHY
Social engineering is a cyberattack technique that manipulates people into revealing sensitive information or performing unsafe actions. Attackers use methods like phishing emails, fake calls, and impersonation to exploit trust, fear, or curiosity. It targets human behavior rather than computer systems, making awareness and caution important for protection.